I’ve been working on getting internal (on-premise) OutSystems platform servers (version 9) installed, running completely on a red stack (Oracle Linux, Oracle database and Oracle WebLogic). One of the things I wanted to try, was getting the platform server available from the outside world, the internet.
Port forwarding on the firewall
When you enable port forwarding on the firewall, using a port like 8444 for example, that redirects traffic to this port to port 443 on an internal OutSystems platform server, it seems to work. When you add “:8444” to the hostname/URL you enter in Service Studio, Integration Studio, or the URL to your web application, you can work with Service Studio and Integration Studio, but the first problem you will encounter is when you try to login to a web application. After clicking the “Login” button, you get redirected to the correct URL, but without the port number (that disappears) and thus you will get an error. You can of course edit the URL and manually add the port number again, but this is not what you want.
After creating a support case with OutSystems, it turns out that using port numbers other than the default 80 (http) and 443 (https) is not supported by OutSystems. This is because the platform servers is not able to determine the used port number (it does not use the URL) and as far as the platform server concerns, it is running on the default ports (no port numbers specified in the URL’s). Probably you could get around this by creating an alternative function to the OutSystems internal function GetOwnerURLPath() used in the default login flow, but you would probably run into problems with ajax redirects, etc.). Anyway, it is not supported by OutSystems.
A little note about using the standard ports 80 and 443: On Unix/Linux systems by default only "root" can start processes that listen on port numbers < 1024. So when you install/configure OutSystems platform server on unix/linux systems, by default it will listen on ports 8080 and 8443. It then configures iptables todo port forwarding on port 80 to 8080 and 8443 to 443.
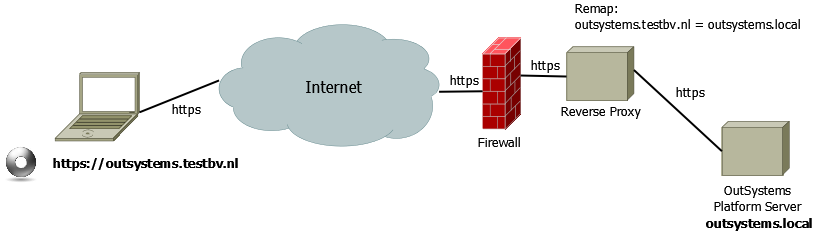
Using a reverse proxy
What is supported by OutSystems is the use of a reverse proxy (see OutSystems documentation). This way users connect to the reverse proxy server from the internet, and the reverse proxy will redirect the request to the OutSystems platform server. For my testing I have installed the Apache Traffic Server (ATS) and configured it to get map external URL’s to the internal platform servers, both http and https.
You can use the Apache Traffic Server other purposes that just redirecting the http(s) traffic, but for this post I just talk about remapping the externally used URL to an internal (on-premise) URL.
Basic configuration of Apache Traffic Server
To get the Apache Traffic Server (ATS) to do its remapping task, first we will need to alter the basic configuration a bit. In my installation of ATS, the configuration files are stored in the directory /etc/trafficserver so if I mention the editing of a configuration file, it will most likely be found in this directory.
First set the port number(s) on which to have the ATS listen. Edit the configuration file records.config en change/set the default port numbers for http and https and make ATS maintain the original host header of the http(s) request. Make sure the configuration parameters proxy.config.http.server_ports and proxy.config.url_remap.pristine_host_hdr look like this:
CONFIG proxy.config.http.server_ports STRING 443:ssl 80 CONFIG proxy.config.url_remap.pristine_host_hdr INT 1
SSL certificate
To be able to use https, an SSL certificate needs to be installed and configured within ATS. As I’m setting up this environment for testing purposes, I create a self-signed certificate that I will use.
So first let’s create a self-signed certificate:
mkdir certificates cd certificates openssl genrsa 2048 > host.key Generating RSA private key, 2048 bit long modulus .........+++ .............................................................................................................................................+++ e is 65537 (0x10001) openssl req -new -x509 -nodes -sha256 -days 3650 -key host.key > host.cert You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [XX]:NL State or Province Name (full name) []:Utrecht Locality Name (eg, city) [Default City]:Utrecht Organization Name (eg, company) [Default Company Ltd]:testbv Organizational Unit Name (eg, section) []: Common Name (eg, your name or your server's hostname) []:*.testbv.nl Email Address []:marcel@testbv.nl openssl x509 -noout -fingerprint -text < host.cert > host.info cat host.cert host.key > host.pem chmod 400 host.key host.pem
Now let’s copy the certificate and private key to be used by the Apache Traffic Server (ATS).
cd /etc/trafficserver mkdir {certs,keys} chown ats:ats {certs,keys} cp ~/certificates/host.key keys/ cp ~/certificates/host.pem certs/ chown ats:ats {keys/host.key,certs/host.pem}
Edit the ATS configuration file records.config to configure the location of certificate and private key. The parameters proxy.config.ssl.server.cert.path and proxy.config.ssl.server.private_key.path should be altered and I commented out (put a # in front of it) the parameter proxy.config.ssl.server.cipher_suite because my browser did have problems with the cipher suites that were configured here.
CONFIG proxy.config.ssl.server.cert.path STRING /etc/trafficserver/certs CONFIG proxy.config.ssl.server.private_key.path STRING /etc/trafficserver/keys CONFIG proxy.config.ssl.client.verify.server INT 0 CONFIG proxy.config.ssl.client.CA.cert.filename STRING NULL #CONFIG proxy.config.ssl.server.cipher_suite
The last part of getting the SSL certificate configured, is to add the (file)name of the certificate to the configuration file named ssl_multicert.config.
dest_ip=* ssl_cert_name=host.pem
Mapping externally used URL to internal URL
To map the externelly used URL to the internal URL, the file named remap.config (on my installation it is stored in /etc/trafficserver) needs to edited. You should add 2 lines, one for redirection of http requests and the other for https requests, using the following format:
map http://<external URL>/ http://<internal URL>/ map https://<external URL>/ https://<internal URL>/ for example: map http://outsystems.testbv.nl/ http://outsystems.local/ map https://outsystems.testbv.nl/ https://outsystems.local/
Don’t forget the slash (“/”) directly after the URL. Without it, the remapping won’t work!
Now restart you Apache Traffic Server (ATS) and see if the remapping works. To troubleshoot, checkout the logfiles error.log and squid.blog, that on my test system could be found in /var/log/trafficserver.
Because squid.blog is a binary formatted logfile, you should use traffic_logcat to see its contents:
traffic_logcat /var/log/trafficserver/squid.blog
Short URL for this post: goo.gl/owHIOP
This article on Quobell website